Massive Malware Campaign Targets Developers with Fake AI Tooling Sites and Malicious Google Ads
March 18, 2026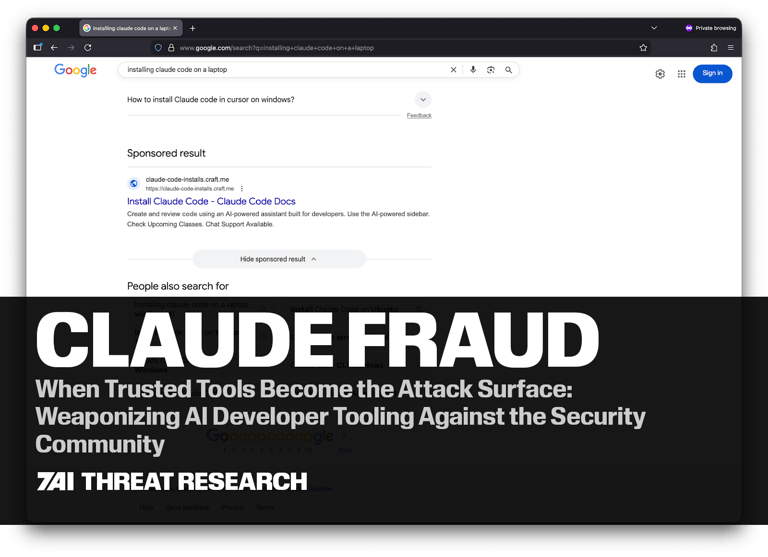
Attackers lure users with cloned official installation pages and malicious sponsored search ads, prompting a curl | bash command that fetches payloads from attacker servers.
Claude Fraud is a multi-variant malware campaign targeting developers and security professionals by abusing trusted AI tooling brands like Claude.ai and Claude Code to deliver malware.
Malicious Claude Code install guides are spread in Google search results as sponsored links under a scheme named InstallFix.
Context notes indicate StepSecurity first reported the issue, with the package maintainer notified and the packages deprecated; public analyses are available through Sonatype and other security sources.
7AI’s approach correlates process chains, infrastructure signals, and user activity to produce high-confidence detections, with concrete examples on macOS and Windows showing rapid SOC ingestion.
Anthropic fixed a prompt-injection flaw and is addressing remaining infrastructure vulnerabilities; organizations should audit connected agent integrations.
Indicators of compromise include unusual files, anomalies in Git histories, and scrutiny of external dependencies sourced from repositories.
Payload workflow polls Solana RPCs for wallet memos, parses them as configuration, decodes a base64 URL for a second-stage payload, and executes it in memory on non-macOS systems.
The attack could allow access to conversation history and memory in standard sessions, with elevated risk when enterprise integrations or MCP servers are involved, enabling autonomous data access and API interactions.
MITRE ATT&CK mappings detail techniques across initial access, execution, defense evasion, and C2 for the campaign.
Executive summary warns that trust in AI developer tools expands the attack surface, with attackers leveraging legitimate infrastructure and workflows to blend in.
Native DLL modules (.node files) are dropped to extract credentials, cookies, tokens, and encrypted Chromium secrets from browser profiles.
Summary based on 14 sources
Get a daily email with more Tech stories
Sources

TechRadar • Mar 18, 2026
Infostealers are being disguised as Claude Code, OpenClaw and other AI developer tools
PCMag • Mar 6, 2026
Phony Claude Code Install Guides Trick Vibe Coders Into Installing Malware
Bitdefender Labs
Windsurf IDE Extension Drops Malware via Solana Blockchain